Telegram group Participant:
https://t.me/joinchat/SBX-EEe1ZLozZGRl
Registration:
https://www.eventbrite.com/e/trend-ai-dan-dunia-pendidikan-tickets-192286111937
Telegram group Participant:
https://t.me/joinchat/SBX-EEe1ZLozZGRl
Registration:
https://www.eventbrite.com/e/trend-ai-dan-dunia-pendidikan-tickets-192286111937
Registration LINK https://www.eventbrite.com/e/ms-team-101-tickets-169819180741
Telegram LINK : https://t.me/joinchat/aApXswecbGZjNzc1
Ms Team 101
For University Community (lecturer, Student, staff)
Synopsis :
WAKTU: saturday, 11 September 2021, 10,00 (AM/ Morning)- finish
Tempat : Ms Team dan Skype
Speaker: Rizal Broer Bahaweres
Technical team: herbert, habib, dkk. & Team KKN 207
# Coordinator Software Engineering – Informatics UIN Jakarta
# PIC (Person In Charge) Microsoft Education – UIN Jakarta
# PIC/Operator Kampus merdeka – Teknik Informatika – UIN Jakarta
# Koordinator Gugus Jaminan Mutu FST – UIN Jakarta
# Assessor SPBE <Evaluasi SPBE – Kementerian PANRB>[Kementerian Pendayagunaan Aparatur Negara dan Reformasi Birokrasi – Sistem Pemerintahan Berbasis Elektronik (SPBE) (menpan.go.id)]
# Dosen Pembimbing KKN <Kelompok 207> UIN Jakarta
# Senior Instruktur DTS <Digital Talent Scholarship>-Kominfo-UIN Jakarta
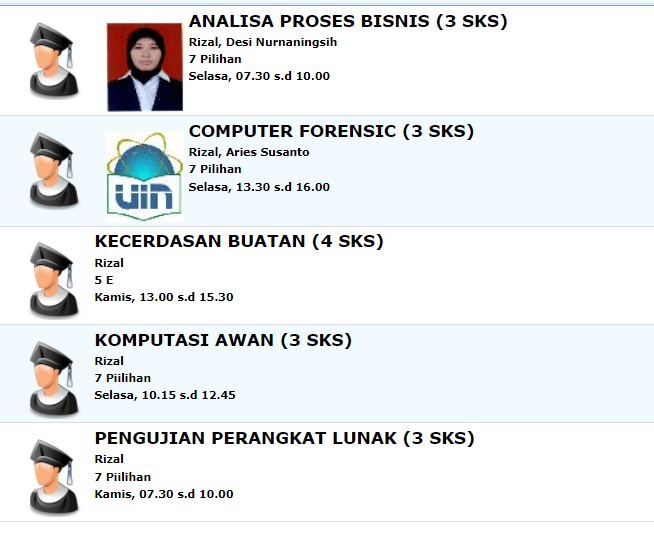
| BPM – Analisa proses Bisnis | https://t.me/joinchat/OfWZWpeAfJhjNTll | |
| Computer/Digital Forensics | https://t.me/joinchat/Uyr8lF3W–5lNWE1 | |
| Kecerdasan Buatan /AI | https://t.me/joinchat/UyTdjPMM3K1lNWY9 | |
| Komputasi Awan/Cloud Computing | https://t.me/joinchat/RJ57Rn-CLU0zMzg1 | |
| Software Testing [penjaminan mutu Perangkat LUNAK(RPL) dan/atau Kualitas RPL] | https://t.me/joinchat/gSRzfnHNZYcwYmY1 |
Silahkan Peserta Perkuliahan JOIN TELEGRAM diatas
Registration : https://www.eventbrite.com/e/lulus-sarjana-3-tahun-aja-tickets-162428597307
Participant telegram link :
https://t.me/joinchat/22A_i54CoOQyNGE9
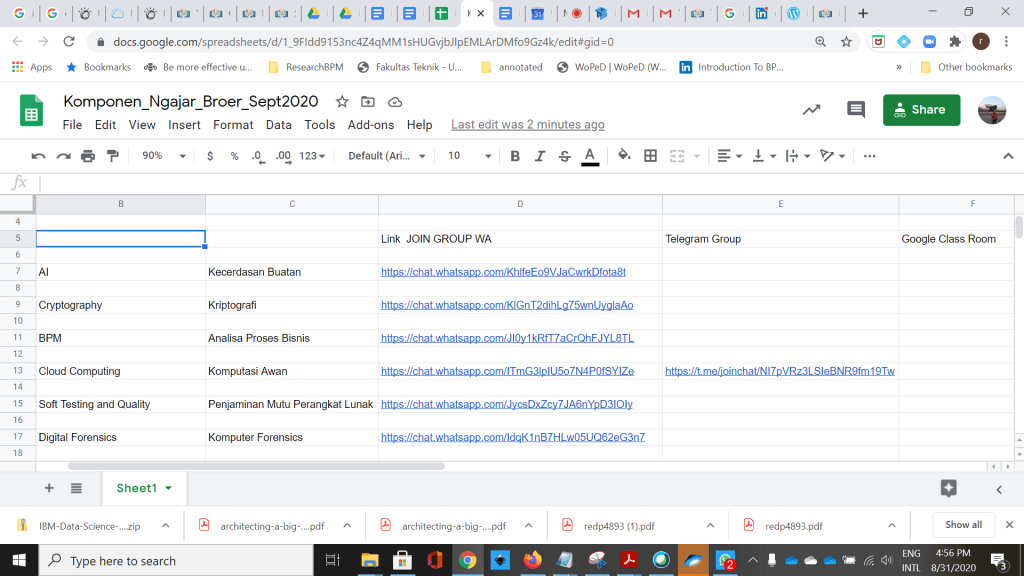
Group WA, Telegram, Google ClassRoom , dll
https://docs.google.com/spreadsheets/d/1_9FIdd9153nc4Z4qMM1sHUGvjbJlpEMLArDMfo9Gz4k/edit?usp=sharing
jupyter notebook/python – data science tutorial – YOUtube
Getting Started With Jupyter Notebook for Python
Jupyter Tutorial
Python For Data Science Training
IPython Notebook best practices for data science
Machine learning in Python with scikit-learn
Scikit Learn – KMeans Clustering Analysis with the Iris Data Set
Machine Learning Tutorial Python – 13: K Means Clustering
// IRISH DataSet
https://www.kaggle.com/uciml/iris , https://www.kaggle.com/tonzowonzo/simple-k-means-clustering-on-the-iris-dataset#
http://archive.ics.uci.edu/ml/index.php
https://en.wikipedia.org/wiki/Iris_flower_data_set
Soal UTS Forensics WhatsAPP
https://drive.google.com/drive/folders/1kEK44K9zR9DOGjv2aNmK-JAnJUnpPf5F?usp=sharing
Soal UTS
whole Suite Test Tools, SBST
https://drive.google.com/drive/folders/1DPSiLpWK3Ote9mio4ik4TY1uOLQppK2V?usp=sharing
File dapat diambil dan dilihat di
https://drive.google.com/drive/folders/1q8fHv39lq2PFsGg4pl-rT2ZDnhN6vNmW?usp=sharing